Introduction
- The System for Cross-domain Identity Management (SCIM) is a standardized protocol that simplifies user identity management in cloud-based applications. SAP Identity and Access Governance (IAG) leverages SCIM to facilitate seamless identity provisioning and de-provisioning, ensuring robust security and efficient user management within an organization.
What is SCIM?
SCIM is designed to make managing user identities in cloud applications and services easier and more standardized. It automates the exchange of user identity information between systems, reducing the administrative burden on IT departments and minimizing errors.
Key Features
- Automation: SCIM automates the creation, updating, and deletion of user accounts across different systems.
- Standardization: It provides a standardized schema and REST APIs for provisioning, making it easier to integrate with various identity providers and applications.
- Security: SCIM ensures that identity information is securely transmitted and maintained, adhering to industry best practices
SAP Identity and Access Governance (IAG)
SAP IAG is a comprehensive solution for managing user identities, access rights, and compliance across SAP and non-SAP environments. It helps organizations streamline their identity management processes, ensuring that users have the appropriate access rights while maintaining compliance with regulatory requirements.
Integration with SCIM
- The integration of SAP IAG with SCIM allows for automated user provisioning and de-provisioning, enhancing the efficiency and security of identity management processes.
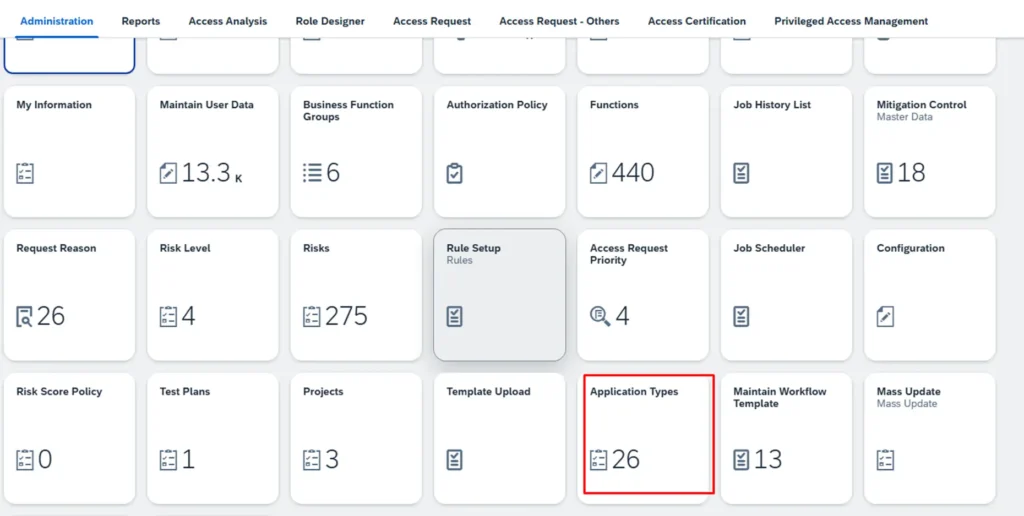
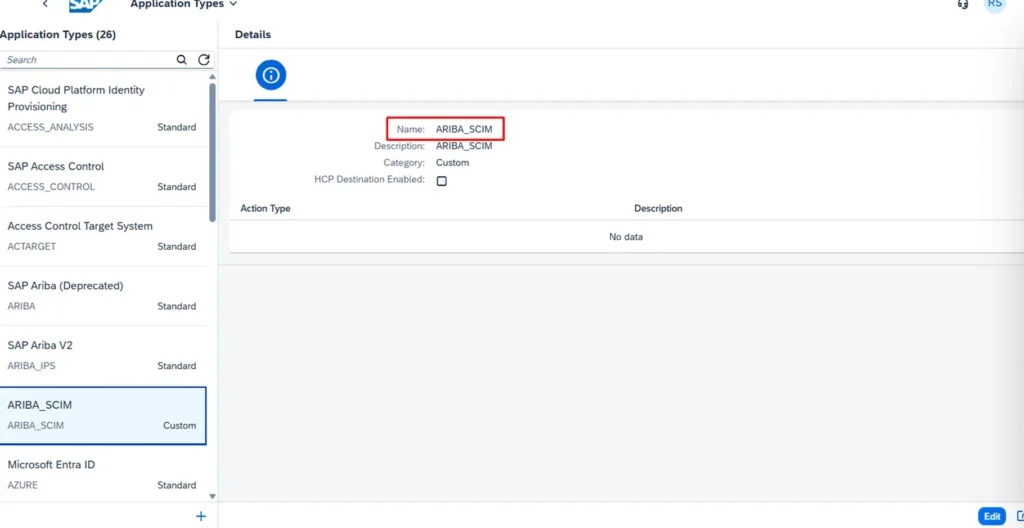
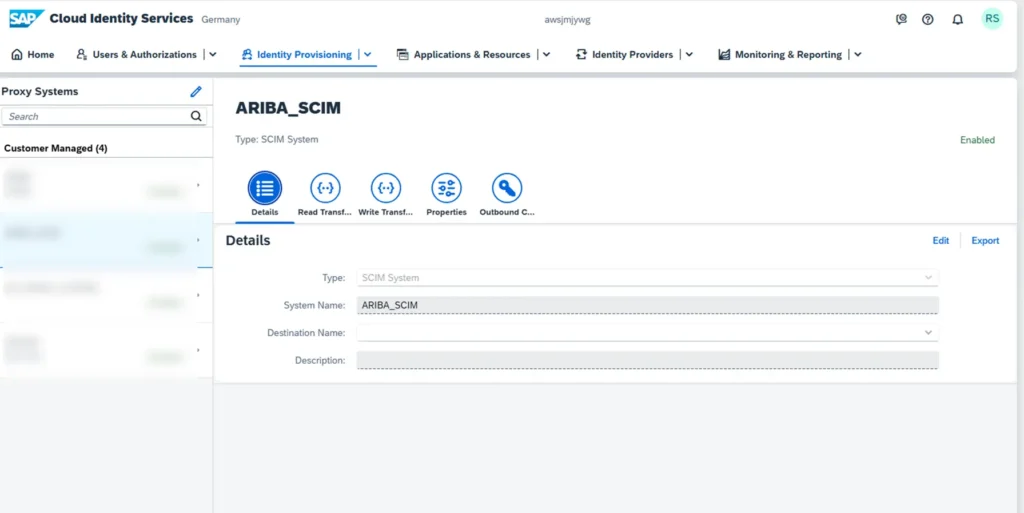
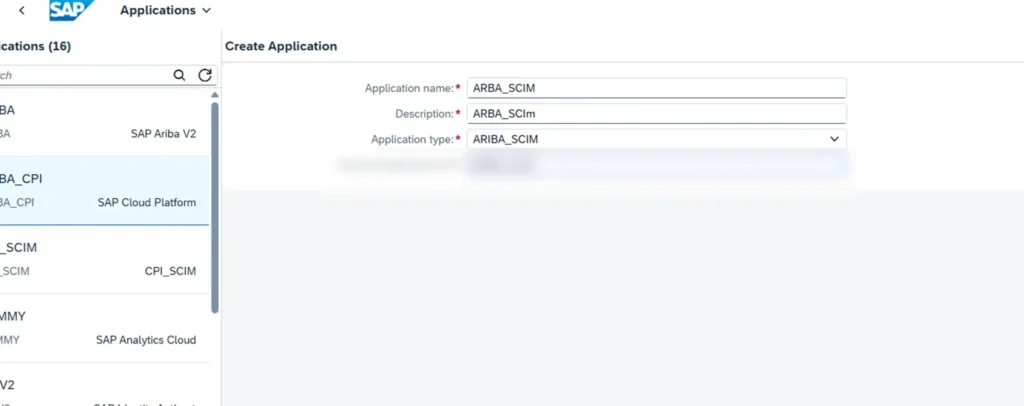
Setting Up SCIM in SAP IAG
Prerequisites:
Before setting up SCIM in SAP IAG, ensure that the following prerequisites are met
- Access to SAP IAG and the necessary administrative privileges.
- Familiarity with the SCIM protocol and its REST APIs.
- Configured identity provider that supports SCIM
Steps
Best Practices for Using SCIM in SAP IAG
1.Regular Monitoring
Continuously monitor the SCIM logs and reports to ensure that user provisioning and de-provisioning processes are running smoothly. Address any errors or issues promptly to maintain system integrity
2.Security Considerations
Implement strong authentication and authorization mechanisms for SCIM endpoints to prevent unauthorized access. Regularly review and update security configurations to align with the latest best practices.
3.Compliance and Auditing
Implement strong authentication and authorization mechanisms for SCIM endpoints to prevent unauthorized access. Regularly review and update security configurations to align with the latest best practices.
Conclusion
Integrating SCIM with SAP IAG offers significant advantages in terms of automation, standardization, and security for identity management. DataNub Technologies ensures to provide best practices which help our customers in managing business risk through our consulting service and implementation of the services & solutions.

